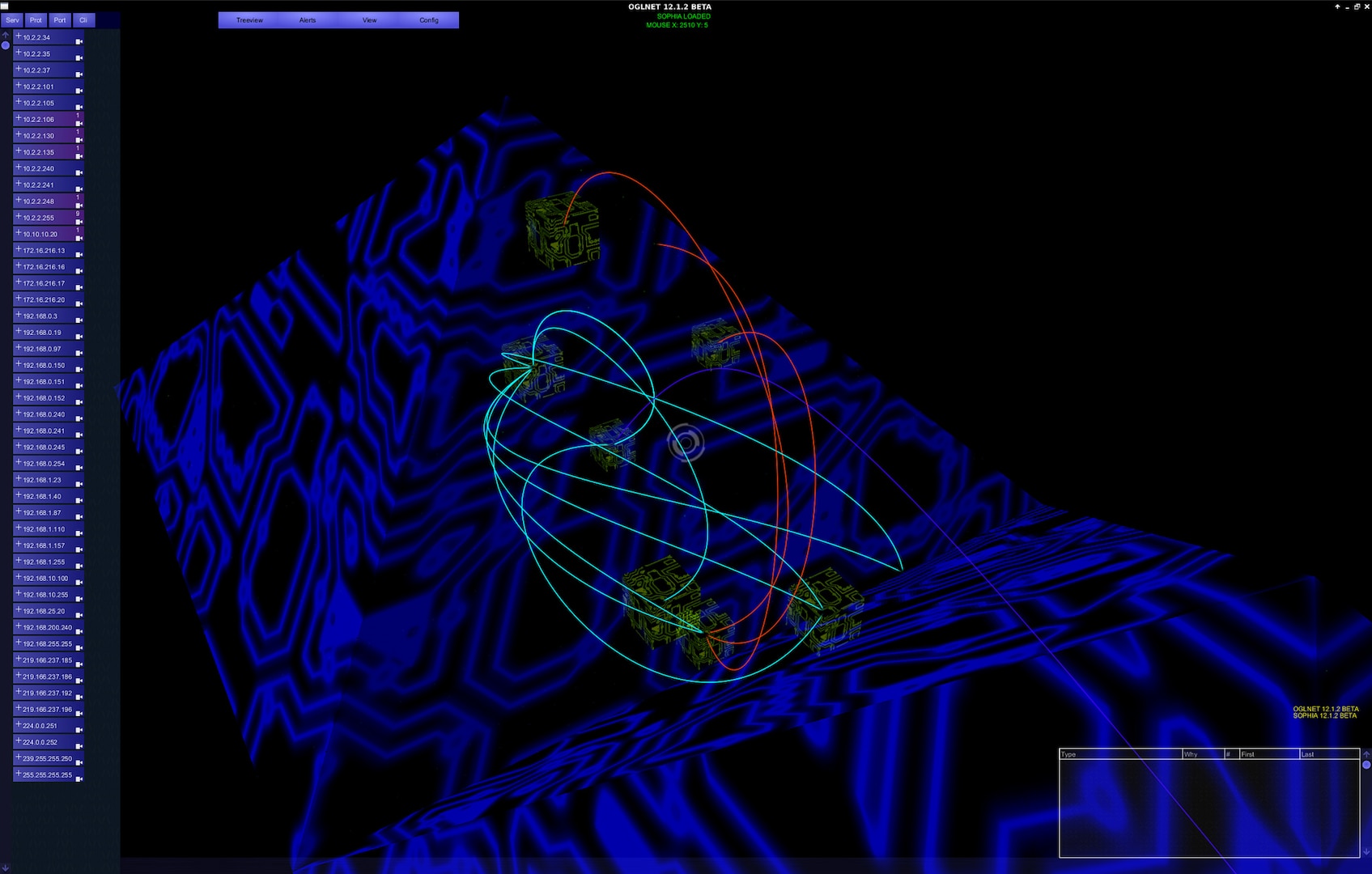
Electronics | Free Full-Text | Research on Cyber ISR Visualization Method Based on BGP Archive Data through Hacking Case Analysis of North Korean Cyber-Attack Groups
XM Cyber acquires continuous end-to-end cybersecurity assessment startup Cyber Observer - SiliconANGLE

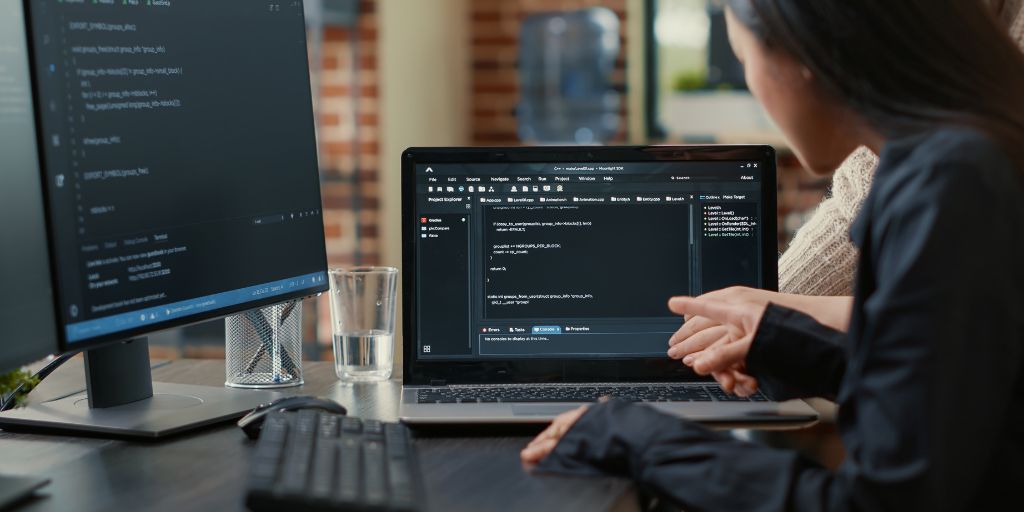
Cyber Security, Information, Communication, Command and Control and Software Systems | CCDC AvMC Program Office for the GTRI UARC Contract

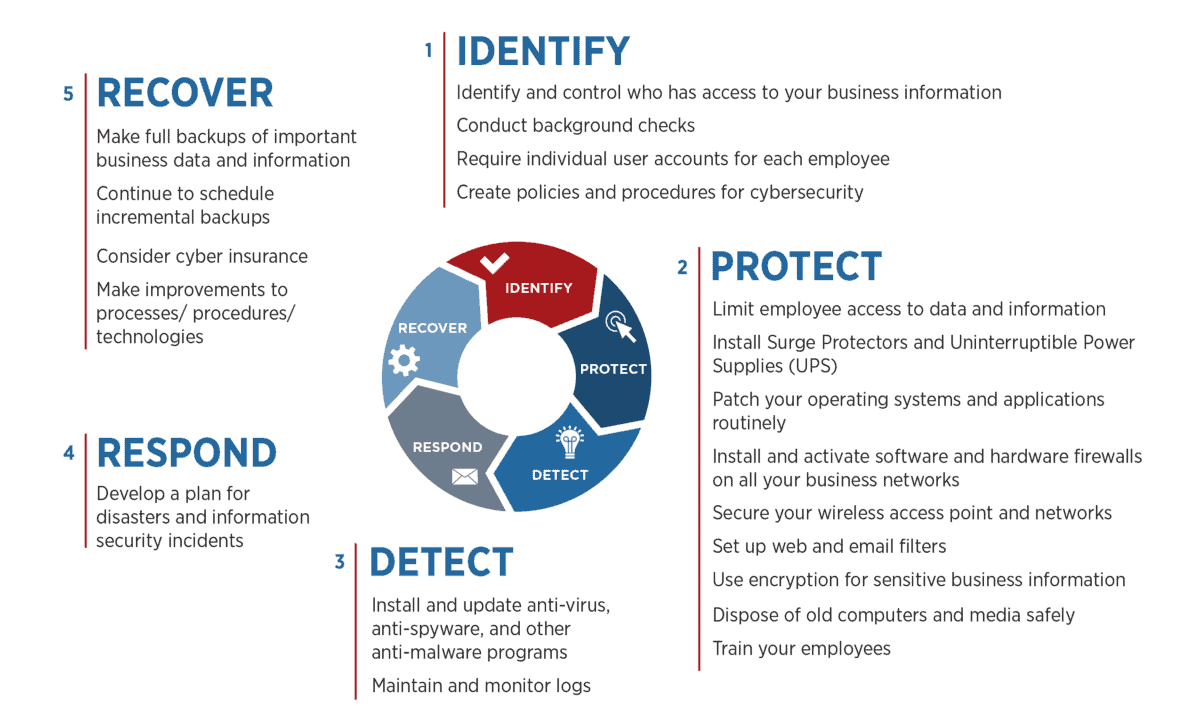
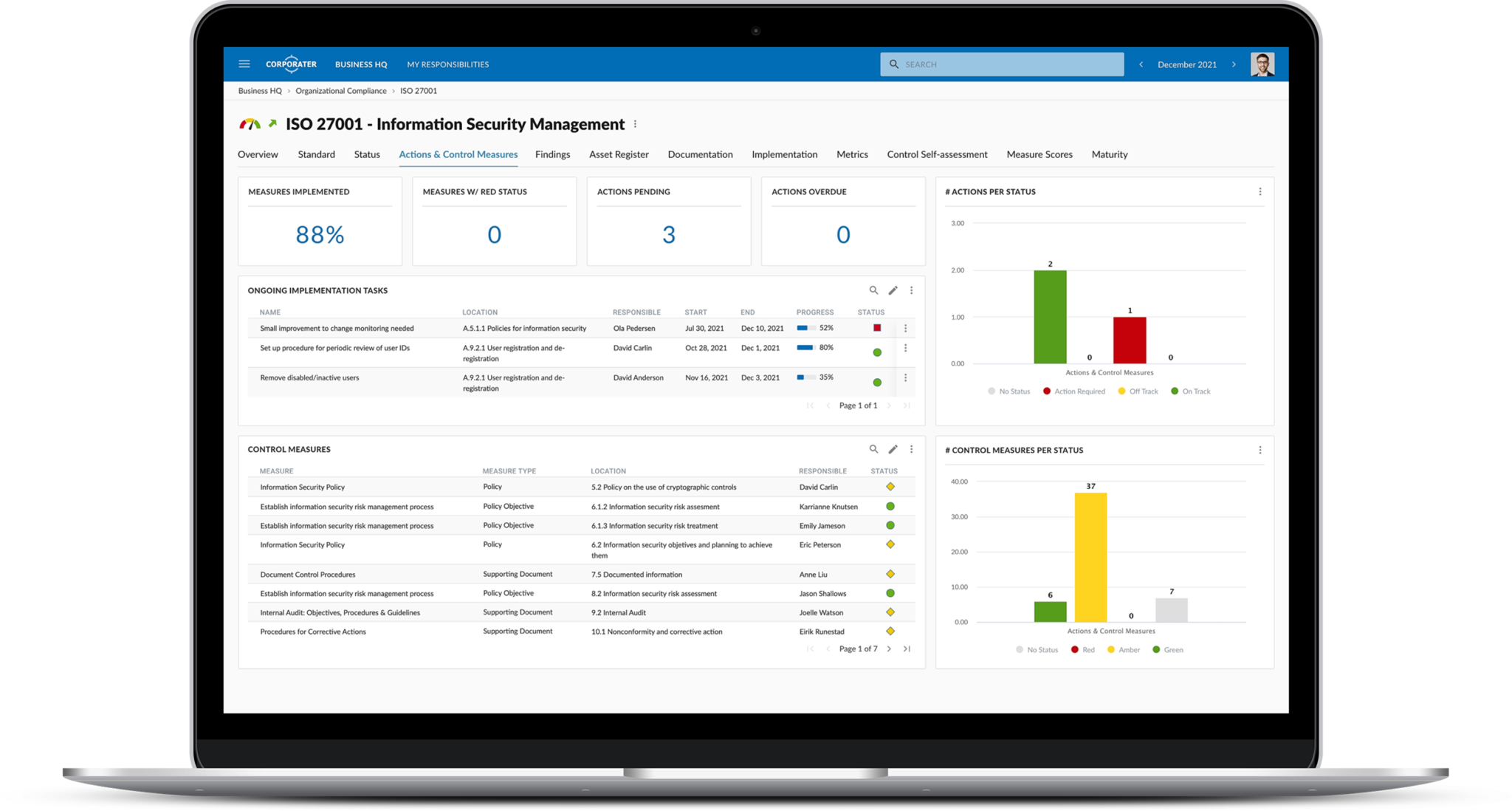
The Importance of Implementing an Effective Cyber Security Management System: The Asset Guardian Solution - Asset Guardian Solutions Limited










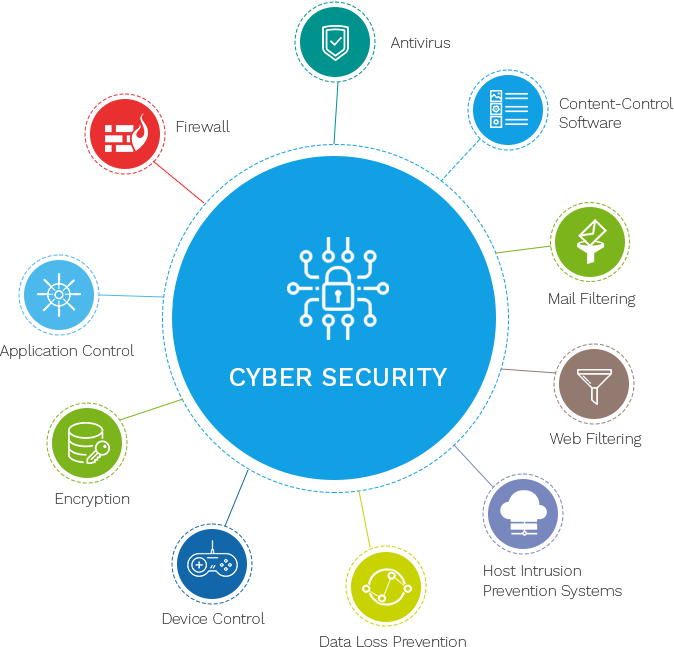
![20 Top Cyber Security Tools in 2023 [Most Powerful Tools] 20 Top Cyber Security Tools in 2023 [Most Powerful Tools]](https://intellipaat.com/blog/wp-content/uploads/2021/06/Top-20-Cyber-Security-Tools-Big.png)